Threat-Informed TPRM
Proactively Manage and Reduce Vendor Cyber Risk
Transform how your team identifies, prioritizes, and acts on real-world cyber threats across your entire vendor ecosystem with a unified, continuous workflow.
Traditional TPRM is Reactive and Slow
Traditional programs rely on manual, periodic questionnaires that only provide a static snapshot of security. With vendor compromises costing an average of $4.9 million, organizations cannot afford to wait 200+ days to discover a breach. Siloed data and limited visibility into shadow vendors leave teams struggling to separate meaningful risks from the noise.
Expect More From Your TPRM
Identify compromises and vulnerabilities across your ecosystem using automatic vendor discovery and confidence scores.
Prioritize what matters by combining technical security signals with business context, like data access and criticality, to focus on the highest-impact threats.
Respond with confidence and Instantly understand your “blast radius” during an incident and use guided workflows to document response efforts for regulatory compliance.
Gain Unified Visibility and Real-Time Risk Reduction
Real-Time Vendor Risk Intelligence
Timely Visibility into Risk
Focus on what matters
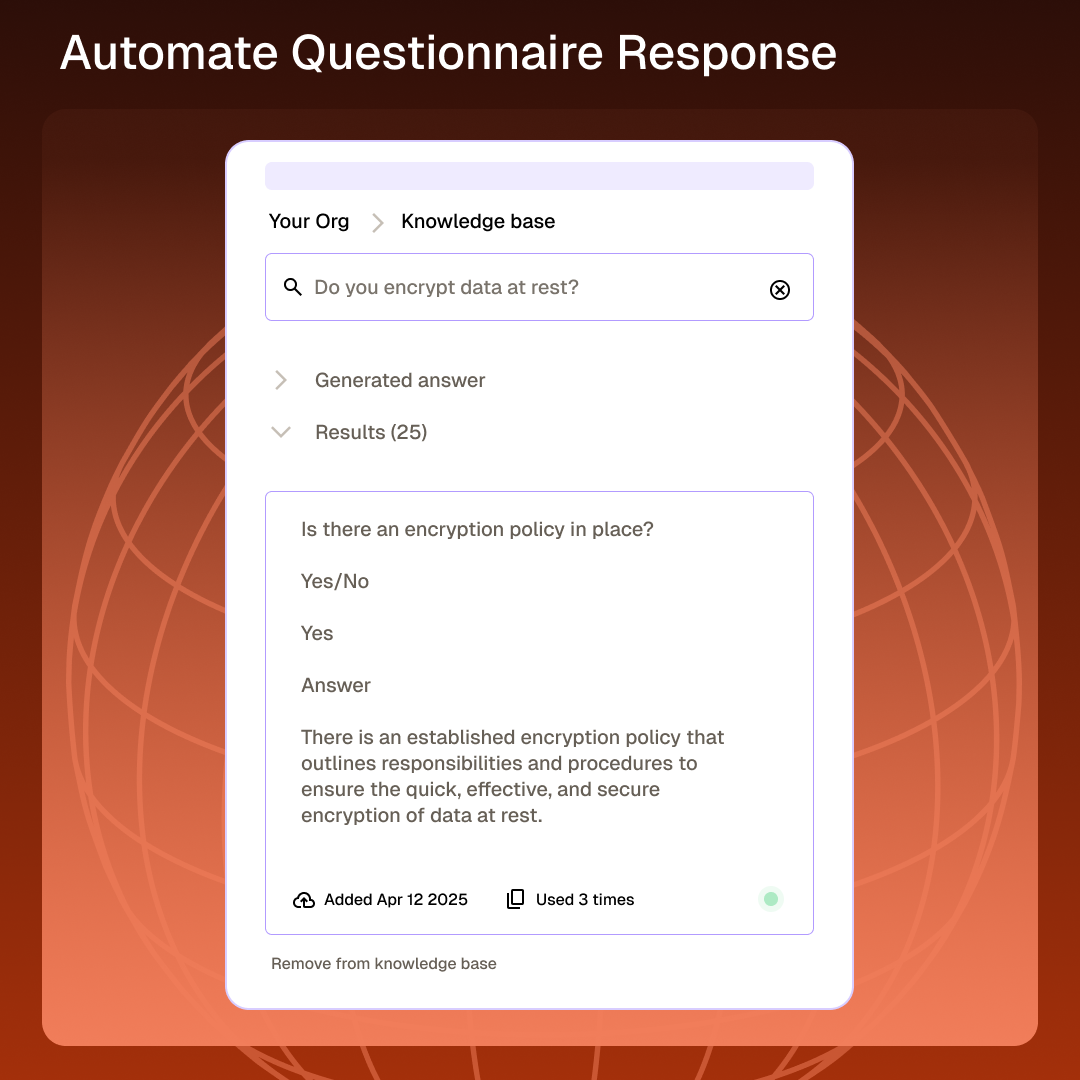
Reduce the back-and-forth
Empower Your Team to Lead with Timely and Accurate Data

Move from manual, reactive tracking to a proactive stance that reduces vendor friction and delivers clear, defensible risk reduction.
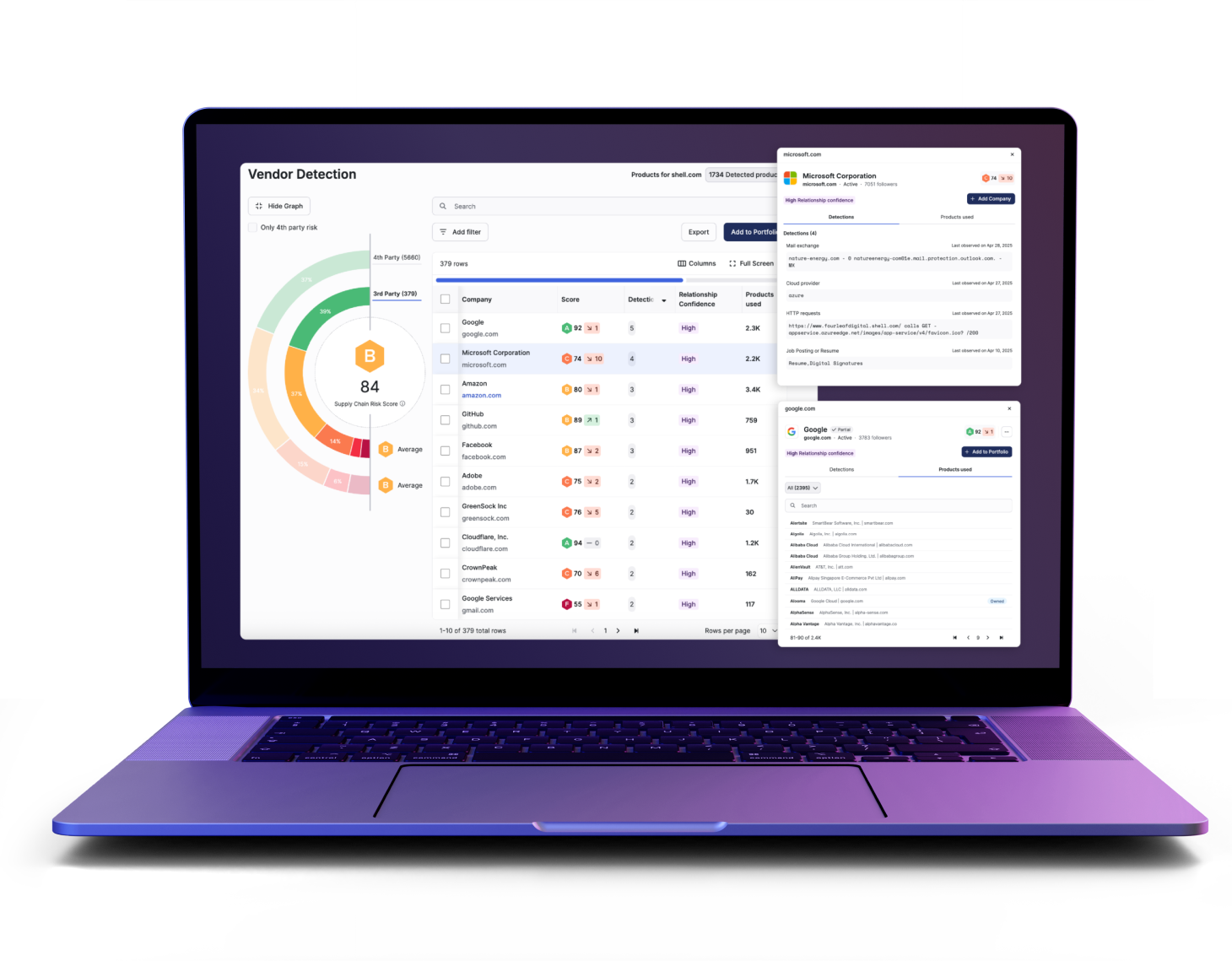
Discover – Third Party Vendor Ecosystem
Automatically detect unknown vendors and map your extended attack surface, including 4th-party concentration risks.

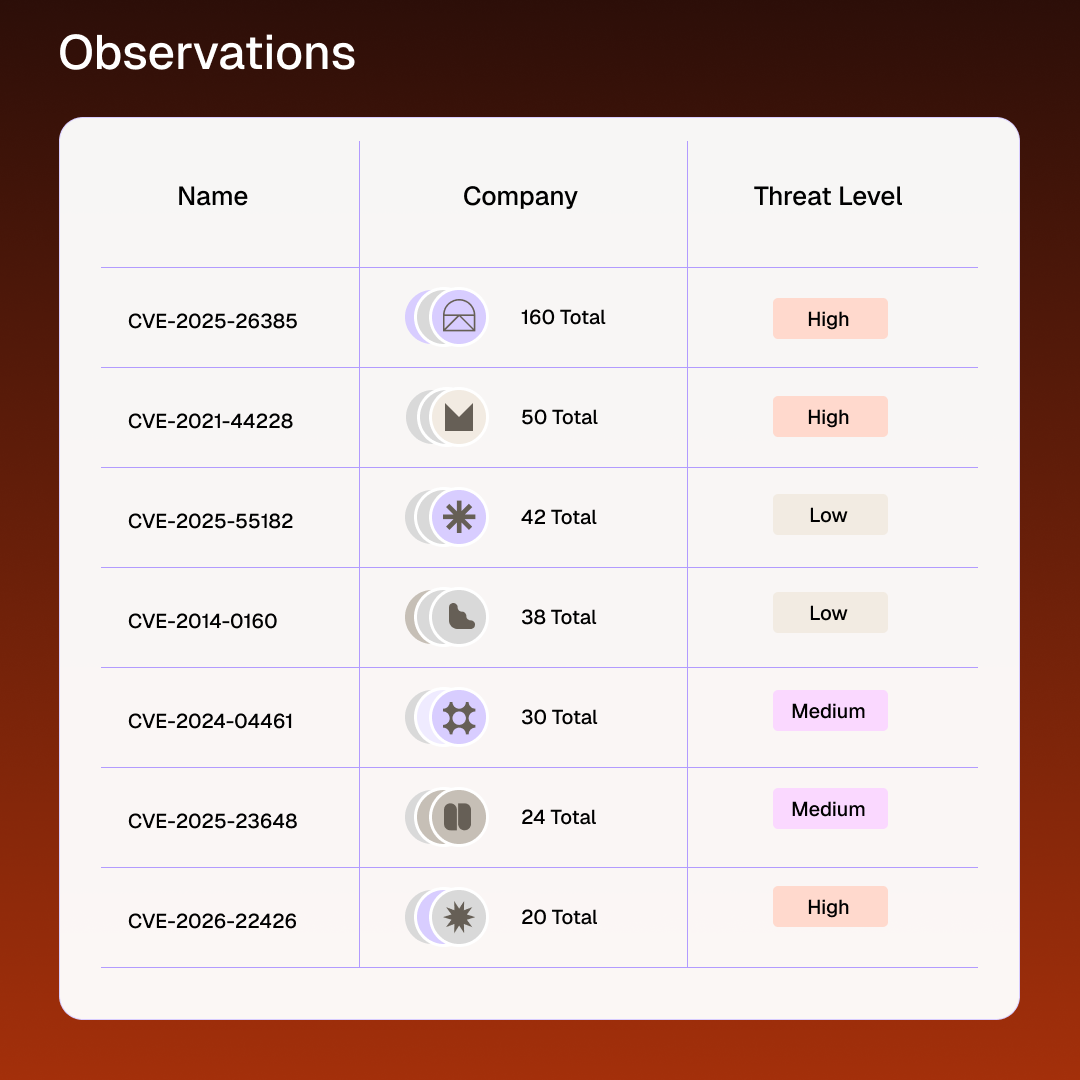
Prioritize – Threat-informed Third Party Risk Management
Apply policy-driven filters to security signals to isolate high-criticality issues, such as vulnerabilities on vendors with PII access.
Engage – Collaborate with Third Parties
Eliminate email friction by using pre-managed contact lists and the Exchange Hub to request remediation or documentation directly in-platform.
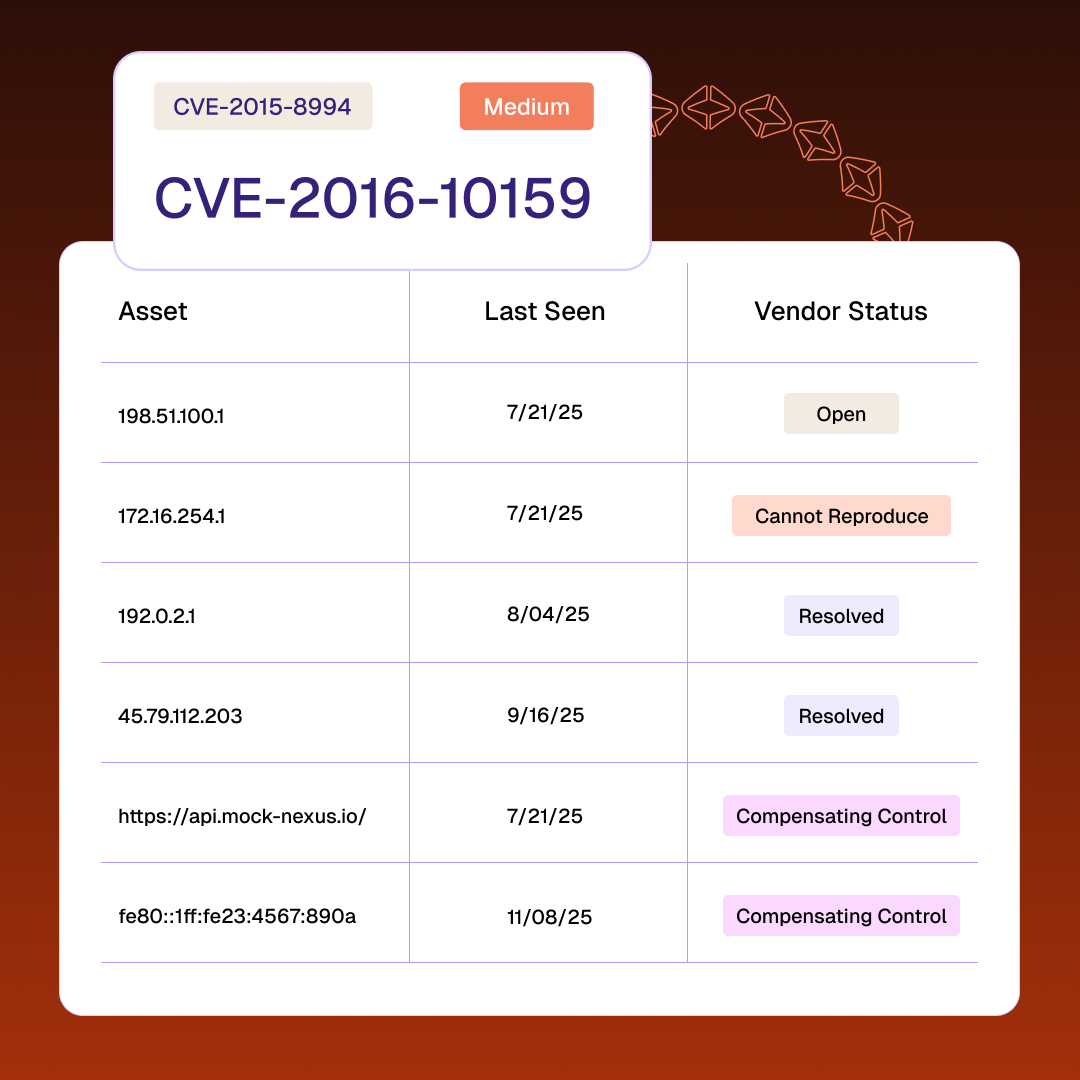
Resolve – Track Vendor Remediation
Map live threat intelligence to your ecosystem to generate executive insights and track vendor remediation through to completion.
Frequently Asked Questions (FAQs)
Everything you need to know about starting your journey with TITAN Secure.
Find more answers in our help centerWhat is Threat-Informed TPRM?
Threat-Informed TPRM is a risk management approach that uses real-time intelligence and adversary tactics to prioritize assessments based on actual threats rather than generic compliance checkboxes.
How does Automatic Vendor Detection work?
It surfaces unknown 3rd and 4th-party vendors and maps them to your supply chain, giving you visibility into your extended attack surface.
Can I communicate with vendors directly in the platform?
Yes, the Exchange Hub allows for “many-to-many” engagement and automated outreach to all impacted vendors regarding an incident.
How does this help with board reporting?
Dynamic reporting and AI-driven summaries translate technical findings into defensible, business-oriented insights for leadership and board meetings.
Does this replace my current GRC tool?
TITAN Secure acts as a unified “System of Record” that can integrate with existing TPRM platforms like ServiceNow, OneTrust, and ProcessUnity.